How much of cybersecurity today is real protection, and how much is marketing hype? This is a question that MSPs and their clients wrestle with every day. Luckily, MSP GLOBAL brought together three tell-it-like-it-is experts to look at the realities and share their advice and best practice list.
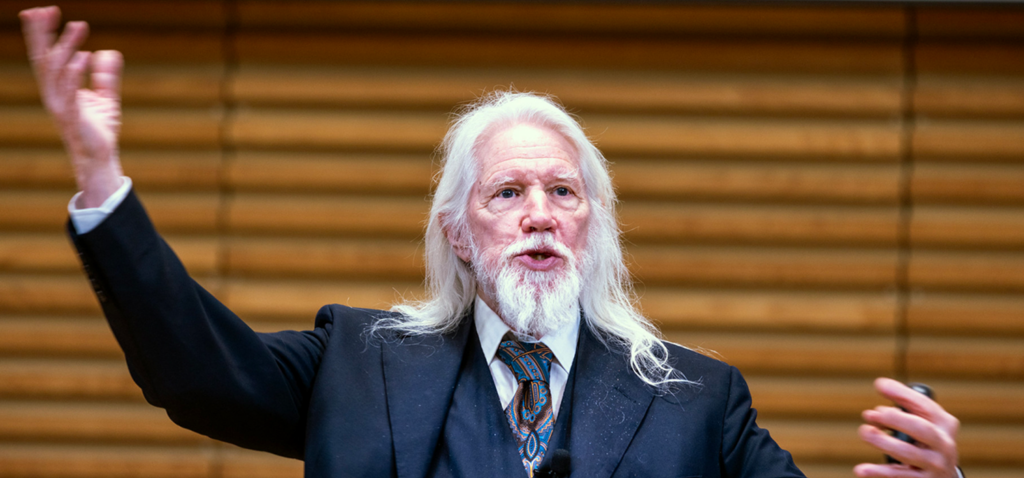
This latest episode of Spill the I-Tea—the MSP GLOBAL Podcast—is a must-watch (or listen, especially if you’re driving) for the entire IT community. You’ll love this panel: famous (well, infamous) hacker Jesse Tuttle, also known as “Hackah Jack”, knows a thing or two about cybercrime. He’s been on the FBI’s Most Wanted List, and now he’s an ethical threat actor for APT2 Labs. Who better for a frank conversation about real-life cybersecurity, right?
Jesse is joined by Brook Lee (VP Community and Channel for Lionguard) and Marcus Gregory (Head of Distribution Partnerships, Spain, for Blackwall) in conversation with Mart Virkus (Head of Marketing at Patchstack).
This conversation highlights a gap that many MSPs recognize: the difference between the perception of security and the reality of defending against increasingly efficient threat actors.
From testing the effectiveness of common security stacks to debating whether “all-in-one” solutions can ever work, the session unpacks the practical challenges MSPs face when building security services for their customers.
For more cybersecurity expertise and insights, join the MSP Community Intelligence Webinar on April 30 where the focus is on security and compliance. Sign up for free.
Five ways for MSPs to evolve their cybersecurity strategies
Stop trusting single-tool security
If you’re still relying on one platform to cover everything, you’re leaving gaps—whether you realize it or not. No single tool can defend against every attack vector, despite what the marketing might suggest.
Real security requires layers of firewalls, endpoint protection, vulnerability management, monitoring, and user awareness into a system that works together. Each layer closes a different gap, and that cumulative effect is what makes the difference.
Attackers don’t try to break strong systems—they look for the easiest way in. If your environment forces them to push through multiple barriers, they’re far more likely to move on. For MSPs, that’s the core principle: defense-in-depth will always outperform convenience.
Cut through the marketing noise
Cybersecurity marketing thrives on simplicity, but real-world environments are anything but simple. Clients are operating across hybrid systems, legacy infrastructure, and evolving threats—so the idea of a single “complete solution” rarely holds up in practice.
That’s where MSPs need to lead the conversation. Move beyond vendor language and explain security in practical, honest terms. Be clear about what tools can do, where the gaps are, and how different controls work together.
This level of transparency doesn’t weaken your position—it strengthens it. It builds trust, sets realistic expectations, and prevents security from becoming a superficial box-ticking exercise.
Build a truly integrated stack
Adding more tools can improve protection, but only if they’re designed to operate as a cohesive system. Poor integration creates blind spots, overlaps waste time and resources, and conflicts can reduce visibility at exactly the wrong moment.
The goal isn’t to assemble a collection of “best-in-class” products in isolation. It’s to design a security ecosystem where each component complements the others and contributes to a clear, unified view of risk.
For MSPs managing multiple clients, consistency is critical. A well-structured, interoperable stack is far easier to scale, manage, and secure than a fragmented one built tool by tool.
Assume you are a target—no matter your size
Cybercriminals are driven by efficiency, not prestige. They’re not necessarily chasing the biggest brand—they’re looking for the quickest, most repeatable path to a payday.
With automated tools, attackers can scan for known vulnerabilities, identify weak defenses, and deploy the same exploit across dozens or hundreds of organizations in a short space of time. Smaller businesses often become prime targets simply because they’re easier to compromise.
For MSPs, this raises the stakes. Every client, endpoint, and connection in your ecosystem represents a potential entry point. Security cannot be tiered by size—it has to be consistently strong across the board.
Don’t try to do everything yourself
Building a fully in-house security capability is resource-intensive, and for many MSPs it’s simply not viable to cover every discipline internally. Skills are scarce, costs are high, and the threat landscape evolves too quickly to manage in isolation.
Strategic partnerships are what make modern security delivery possible. The right vendors and specialist providers allow you to extend your capabilities while maintaining focus and efficiency.
However, those partnerships need to be grounded in transparency. You need to understand exactly what each solution delivers, where its limitations lie, and how it fits into your broader stack.
When that alignment is right, you can deliver something far more valuable than any single tool—a layered, realistic, and scalable security model that your clients can depend on.
Join the conversation at MSP Global 2026
At MSP GLOBAL 2026, MSP leaders, vendors, and security experts will once again come together to explore the biggest opportunities and challenges facing the channel.
If cybersecurity, AI, Cloud platforms, and new service models are reshaping your business, this is where the next ideas—and partnerships— begin.
Register now to be part of the next MSP GLOBAL—just sign up for the newsletter to get your free code.